 Any organization above $1 billion in revenues and more than 5000 employees can be considered as a large enterprise. Most Large Enterprises have different type of firewall deployment needs such as
Any organization above $1 billion in revenues and more than 5000 employees can be considered as a large enterprise. Most Large Enterprises have different type of firewall deployment needs such as
- Internet-Edge Firewalls
- Data Center Firewalls
- Branch Office Firewalls
This segment also becomes more interesting because they generally have both Network & Security Operations teams, which access those firewalls. Users of different teams have different expectations from the Firewall Manager.
Another factor that can play an important role is other Network Security appliance such asIntrusion Prevention Systems (IPS). If bought from the same vendor its possible that the Firewall Management solution will also have to manage IPS. As you would have imagined by now Firewall Management needs of a Large Enterprises will differ a lot from those of Small and Medium Size business or Distributed Branch type of businesses.
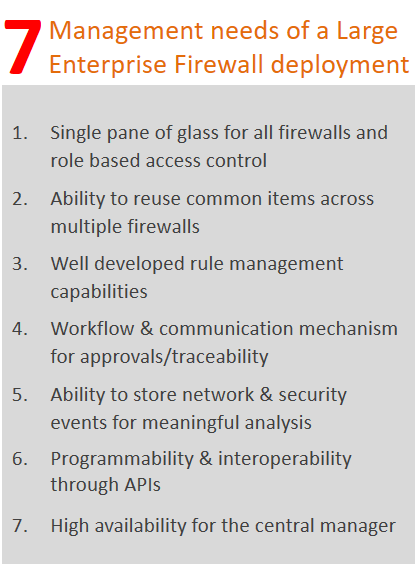
1. Single pane of glass to organize and manage firewalls
 This one is obvious. Large Enterprises typically have many geographically distributed firewalls and its possible that a security central team would want to some firewall policies. In order for these teams to effectively do that they need Central Firewall Manager, which allows them to reach any firewall without having to ask permissions.
This one is obvious. Large Enterprises typically have many geographically distributed firewalls and its possible that a security central team would want to some firewall policies. In order for these teams to effectively do that they need Central Firewall Manager, which allows them to reach any firewall without having to ask permissions.
At the same time these organizations have local network security staff, which may be tasked with managing configurations of these firewalls. In short, the large enterprises need a central manager, which can act as single pane of glass for all the firewalls but that the same time can provide Role Based Access Control to various users so that they can do their jobs effectively.
2. Ability to reuse common items across multiple firewalls
 When you have to manage many firewalls, you would definitely want to reuse configuration elements such as Objects, Services, and Access Rules etc. across multiple firewalls. Most common Firewall Management solutions provide ability to reuse configuration elements but only good ones will have ability to track usage of these components so that you can figure out where they are used and how they are being used.
When you have to manage many firewalls, you would definitely want to reuse configuration elements such as Objects, Services, and Access Rules etc. across multiple firewalls. Most common Firewall Management solutions provide ability to reuse configuration elements but only good ones will have ability to track usage of these components so that you can figure out where they are used and how they are being used.
The best Firewall Management appliances don’t stop by providing reusability of firewall rule related items, they go beyond that by identifying what else is commonly used and providing reusability for that. Example could be Services, Profiles, Schedules or Templates. Why ask users to do create same items again and again when it can be done once and used multiple times.
3. Well developed firewall rule management capabilities
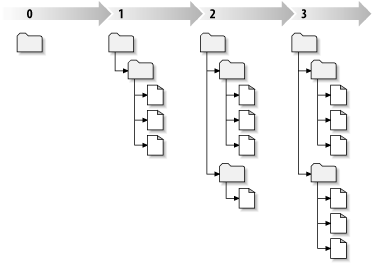 If you can’t organize and manage your rules effectively using Firewall Management appliance then what’s the point of paying for it? Make sure you check for features like Rule grouping/sections, Version control & Rollback, Usage Statistics and Rule Expiry. Actually, I just realized that I could write an entire post about it so I will do that in the future :).
If you can’t organize and manage your rules effectively using Firewall Management appliance then what’s the point of paying for it? Make sure you check for features like Rule grouping/sections, Version control & Rollback, Usage Statistics and Rule Expiry. Actually, I just realized that I could write an entire post about it so I will do that in the future :).
Among all these features, version control and ability to rollback specific rule or user changes is critical. It’s possible that your enterprise has review and approval process for making firewall changes. But when you have so many folks accessing and managing your numerous firewalls you would want to know is who has done what and when. There is always a possibility of someone making a configuration mistake or change, which you want to revert. At such times you would want to go back to previous known good configuration without only that specific users that specific rule change. This is only possible when your firewall management appliance has version control for your firewall rules.
4. Workflows/communication for approvals & traceability
 Most large enterprises have many network and security administrators. In many cases the configuration changes are proposed by one team, approved by a different team, and implemented by another one. If the Firewall Management solution doesn’t have mechanism to orchestrate these workflows and communication then it becomes difficult to manage operations effectively. So make sure you assess for this feature when you evaluate your next Firewall Manager.
Most large enterprises have many network and security administrators. In many cases the configuration changes are proposed by one team, approved by a different team, and implemented by another one. If the Firewall Management solution doesn’t have mechanism to orchestrate these workflows and communication then it becomes difficult to manage operations effectively. So make sure you assess for this feature when you evaluate your next Firewall Manager.
Another thing you should check is ability of your Firewall Manager to inter-work with Third Party trouble ticketing/orchestrating systems so that you can pass information to and fro, which I will discuss in the another must have feature i.e. Programmability.
5. Ability to store network & security events for meaningful analysis
 When you are managing many firewalls that are protecting your organization you are bound to get large number of myriad types of firewall events. It’s also likely that by law your organization will be required to store all firewall events for certain number of days. In most countries I have seen at least 90 days limit. You can always use some other offline storage mechanism but if you really want to understand what’s happening on your firewall you will need to store those firewall events at least for few weeks. Most companies take few months to detect data breaches or cyber security attacks[1].
When you are managing many firewalls that are protecting your organization you are bound to get large number of myriad types of firewall events. It’s also likely that by law your organization will be required to store all firewall events for certain number of days. In most countries I have seen at least 90 days limit. You can always use some other offline storage mechanism but if you really want to understand what’s happening on your firewall you will need to store those firewall events at least for few weeks. Most companies take few months to detect data breaches or cyber security attacks[1].
Ability to store those firewall events is helpful but it doesn’t offer you much if your firewall management appliance doesn’t offer good correlation engine & analytics to make sense of those events. Easy mechanism to drill down and filter the events using various criteria will go long way when you are trying to debug why your CEO/VP isn’t able to download file from his personal Dropbox folder. ;).
Lastly, we all work for someone so there is a high likelihood that you will be required to demonstrate your security effectiveness through status reports. So make sure you have standard in built as well as customer reporting capability to build what you need using the security events on your firewalls.
6. Programmability – Ability to tie-in other solutions with FW Manager
 Because securing network is of paramount importance, most large enterprises have multiple security solutions to cover plethora of security challenges. Majority of the security product vendors understand their product isn’t the silver bullet for solving all security issues Enterprises face. These vendors also understand that if they allow their products to work with other products/systems through APIs it provides more value to their customers. In case of Firewalls, APIs become even more important because they not only help orchestrate the firewalls but also provide mechanism to get information out of the firewalls for further analysis. Imagine, how hard it will be to perform firewall rule analysis or remediation through another system based on the Firewall event?
Because securing network is of paramount importance, most large enterprises have multiple security solutions to cover plethora of security challenges. Majority of the security product vendors understand their product isn’t the silver bullet for solving all security issues Enterprises face. These vendors also understand that if they allow their products to work with other products/systems through APIs it provides more value to their customers. In case of Firewalls, APIs become even more important because they not only help orchestrate the firewalls but also provide mechanism to get information out of the firewalls for further analysis. Imagine, how hard it will be to perform firewall rule analysis or remediation through another system based on the Firewall event?
Now days, you will find various flavors of APIs. You can read more about the API Types in a nice blog but considering the product in question i.e. Firewall I feel REST APIs are the most suitable. So make sure your next Firewall Manager has full-fledged APIs for you to make use of.
7. High Availability
 If you have all that functionality and you are managing all your firewalls using that single Firewall Manager then obviously it would be critical to have high availability for such a solution. High Availability comes in many flavors such as Backup system, which need to bring up when Primary goes down, or Active/Standby solution, in which Standby picks up automatically when Active goes down, or Active/Active, where both systems are working and the second system picks up the load of first one when that goes down.
If you have all that functionality and you are managing all your firewalls using that single Firewall Manager then obviously it would be critical to have high availability for such a solution. High Availability comes in many flavors such as Backup system, which need to bring up when Primary goes down, or Active/Standby solution, in which Standby picks up automatically when Active goes down, or Active/Active, where both systems are working and the second system picks up the load of first one when that goes down.
Most vendors will offer some sort of High Availability but I recommend you at least get Active/Passive one where you don’t have to do anything manually when Active goes down. You never know when the system will go down and its not good idea to rely on humans to switchover when we know that technology for HA mechanism has been in the market for significant time already.
Now those are my top 7 asks from an enterprise grade Firewall Management solution. What do you think?
[1] http://www.zdnet.com/article/businesses-take-over-six-months-to-detect-data-breaches/
No Comments Yet